After attending the JNCIE-SEC bootcamp last week, I saw that one topic was barely mentioned: The way of running OSPF over GRE over IPsec. Since this setup is barely used (because of various reasons) I thought, that this is post-worthy – so here you have a working config (running on Firefly 12.1X47-D35.2
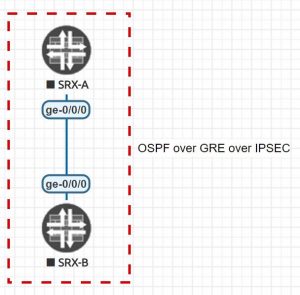
Topology:
Config for Firefly-A:
# General Setup set system host-name Firefly-A set interfaces ge-0/0/0 unit 0 family inet address 172.16.15.1/30 # IPsec Part set interfaces st0 unit 0 family inet address 172.16.16.1/30 set security zones security-zone VPN interfaces st0.0 set security ike proposal ike_aes_128 dh-group group5 set security ike proposal ike_aes_128 authentication-method pre-shared-keys set security ike proposal ike_aes_128 authentication-algorithm sha1 set security ike proposal ike_aes_128 encryption-algorithm aes-128-cbc set security ike policy ike_p1 mode main set security ike policy ike_p1 pre-shared-key ascii-text juniperipsec123 set security ike policy ike_p1 proposals ike_aes_128 set security ike gateway Firefly_B ike-policy ike_p1 set security ike gateway Firefly_B external-interface ge-0/0/0.0 set security ike gateway Firefly_B address 172.19.15.2 set security ipsec proposal ipsec_p2 protocol esp set security ipsec proposal ipsec_p2 authentication-algorithm hmac-sha1-96 set security ipsec proposal ipsec_p2 encryption-algorithm aes-128-cbc set security ipsec policy p2_ipsec proposals ipsec_p2 set security ipsec vpn VPN_To_Firefly_B ike gateway Firefly_B set security ipsec vpn VPN_To_Firefly_B ike ipsec-policy p2_ipsec set security ipsec vpn VPN_To_Firefly_B establish-tunnels immediately set security ipsec vpn VPN_To_Firefly_B bind-interface st0.0 # GRE and OSPF Part set interfaces gr-0/0/0.0 tunnel source 172.16.16.1 set interfaces gr-0/0/0.0 tunnel destination 172.16.16.2 set interfaces gr-0/0/0.0 family inet address 172.16.16.5/30 set security zones security-zone DMZ interfaces gr-0/0/0.0 host-inbound-traffic system-services ping set security zones security-zone DMZ host-inbound-traffic protocols ospf set protocols ospf area 0 interface gr-0/0/0.0
Config for Firefly-B:
# General Setup set system host-name Firefly-B set interfaces ge-0/0/0 unit 0 family inet address 172.16.15.2/30 # IPsec Part set interfaces st0 unit 0 family inet address 172.16.16.2/30 set security zones security-zone VPN interfaces st0.0 set security ike proposal ike_aes_128 dh-group group5 set security ike proposal ike_aes_128 authentication-method pre-shared-keys set security ike proposal ike_aes_128 authentication-algorithm sha1 set security ike proposal ike_aes_128 encryption-algorithm aes-128-cbc set security ike policy ike_p1 mode main set security ike policy ike_p1 pre-shared-key ascii-text juniperipsec123 set security ike policy ike_p1 proposals ike_aes_128 set security ike gateway Firefly_A ike-policy ike_p1 set security ike gateway Firefly_A external-interface ge-0/0/0.0 set security ike gateway Firefly_A address 172.19.15.1 set security ipsec proposal ipsec_p2 protocol esp set security ipsec proposal ipsec_p2 authentication-algorithm hmac-sha1-96 set security ipsec proposal ipsec_p2 encryption-algorithm aes-128-cbc set security ipsec policy p2_ipsec proposals ipsec_p2 set security ipsec vpn VPN_To_Firefly_A ike gateway Firefly_A set security ipsec vpn VPN_To_Firefly_A ike ipsec-policy p2_ipsec set security ipsec vpn VPN_To_Firefly_A establish-tunnels immediately set security ipsec vpn VPN_To_Firefly_A bind-interface st0.0 # GRE and OSPF Part set interfaces gr-0/0/0.0 tunnel source 172.16.16.2 set interfaces gr-0/0/0.0 tunnel destination 172.16.16.1 set interfaces gr-0/0/0.0 family inet address 172.16.16.6/30 set security zones security-zone DMZ interfaces gr-0/0/0.0 host-inbound-traffic system-services ping set security zones security-zone DMZ host-inbound-traffic protocols ospf set protocols ospf area 0 interface gr-0/0/0.0
Hope, that this helps you if you ever have to do this or need to learn this…
Remember – this is just a sample – please use stringer ciphers if possible 😉
The JNCIE-Exam is getting closer and closer…
Hi
Can you please,elaborate which interfaces have ips 172.16.19.x which are mentioned in vpn configs
Thanks
Sorry i mean172.19.16.x
You mean 172.16.16.x?
Depends – the first usable subnet (/30) is the st0-Interface and the next usable is the gre-Interface.