Juniper Open Learning: Using EVE-NG with Juniper Topologies – Slides
Since so many of you asked for it: Of course I can share the Slides 🙂 Here you find the Slides from the Session held on 15.09.2020
Since so many of you asked for it: Of course I can share the Slides 🙂 Here you find the Slides from the Session held on 15.09.2020
Yesterday I played with the OpenVPN Settings in my PfSense at home and thought: Will it be possible to enable IPv6 through my VPN so that I can access my… Read more »
On September 15th 2020 I will host another session with the amazing @JuniperCertify team about EVE-NG and Juniper devices. Reserve your seat here: https://learningportal.juniper.net/juniper/user_activity_schedule_info.aspx?id=157373&activity=11495 Topics are:EVE-NG in IPv6-only mode Creating… Read more »
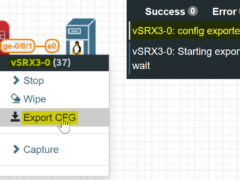
Some time ago I blogged about a custom template for the vSRX 3.0. One drawback was, that the config-export would no longer work, since this is a custom template but… Read more »

Last week I blogged about the virtual Roundtable that we had to discuss our work in the Corona Era. I promised you to share this exciting talk – huge shoutouts… Read more »

If you use the “config export” in your EVE-NG you might have noticed, that there are predefined passwords, that you have to use for this task. If you want to… Read more »

I like the idea of monitoring my EVE-NG Server with my external LibreNMS Server. Setting this up on EVE-NG (Ubuntu 16.04) is relatively easy – even in IPv6 only mode…. Read more »

You should check out the Twitter Handles of the Ambassadors soon. I just had the greatest time discussing the impact on the IT landscape during the COVID-19 pandemic. This Juniper… Read more »
Here you find the vSRX 3.0 custom template for your EVE-NG. Add this file (named vsrx30.yml) to your /opt/unetlab/html/templates/intel/ folder: Don’t forget to include it in your custom_templates file at… Read more »

The newest eve-ng ( 2.0.6-42(+43+44)-PRO // 2.0.3-108-Community) introduces a lot of cool new features for making your daily work easier than ever, that I will cover in the next few… Read more »